In the early days of the internet, hackers built viruses to show off.
Most of the early hackers were teenagers or in their early 20s. The ones who got caught talked about trying to impress the world with their skills.
Nowadays, we have software that is pretty good at detecting a well-built virus. Much of that software—at least at the consumer level—is free.
At the same time our software detection is advancing, the typical hacker is an international criminal. But this criminal is frustrated: Your anti-virus software keeps recognizing his virus or worm.
He would like your help …
What to do?
Hackers are trying to recruit your employees. Maybe even recruit you! Sadly, this “social engineering” succeeds too often. Smart people keep falling for engineering tricks. At times, it almost seems like people are designed to self destruct.
Security experts say social engineering relies on people being people. Human beings have a normal response to social interaction. Of course, hackers leverage these reactions to get past company security.
To get started, the perpetrator must prepare the ground. He/she starts by researching your company. The goal is to find published names of managers and employees in key roles. The perp may also look for recent news about your company’s activity. … such as potential points of entry and weak security protocols, needed to proceed with the attack.

Step number two is to gain the victim’s trust. In other words; “provide stimuli for subsequent actions that break security practices, such as revealing sensitive information or granting access to critical resources.”
In the Realize blog, we have used images of people with their faces concealed as symbolic of hidden activity.
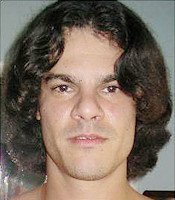
Here is a photo of a real hacker; Albert Gonzalez in 2009 pleaded guilty to helping organize massive credit card thefts.
He was sentenced to prison.
His targets: TJ Maxx, Dave & Buster’s, Heartland Payment Systems, 7-Eleven, Office Max, Boston Market, Sports Authority.
A real “engineer” at work
Social engineering examples
For a clearer picture, let’s walk through this process with some help from HackerNoon. The following examples are from “How Social Engineering is Used to Bypass Your Security…with Ease,” written by Nathan House.
Social Engineering email #1
from: itsecurity@targetcompany.com
to: sarah.jones@targetcompany.com
subject: IT Security
Sarah,
As a new starter to the company, you will need to be made aware of the company’s IT Security policies and procedures and specifically, the employees “Acceptable Use Policy”.
The purpose of this policy is to outline the acceptable use of computer equipment at target company. These rules are in place to protect the employee and target company. Inappropriate use exposes risks including virus attacks, compromise of network systems and services, and legal issues.
This policy applies to employees, contractors, consultants, temporaries, and other workers at target company, including all personnel affiliated with third parties. This policy applies to all equipment that is owned or leased by target company.
Someone will contact you shortly to discuss this with you.
Regards,
IT Security
Targeting ordinary workers
Voice on the phone sounds legit…
The preceding email has laid the hacker’s groundwork. It suggested to a new employee she will soon get an official phone call. Naturally, this sounds normal to anyone working in corporate America. The email does not ask for money or information. It avoids the more obvious flags that identify malicious messages.
All the hacker has to do now is get past the folks answering the phones…
Social Engineering call #8
A couple of hours later, call to the main switchboard of the organization…
Nathan: Hi, could you put me through to Sarah Jones, please?
Reception: Connecting you.
Sarah: Hello, Sales. How can I help you?
Nathan: Hi Sarah. I’m calling from IT Security to brief you on IT security best practices. You should have gotten an email about it.
Sarah: Yes, I got an email about it today.
Nathan: OK, excellent. It’s just standard procedure for all new starters and only takes about 5 minutes. How are you finding things here? Is Everybody being helpful?
Sarah: Yes, thanks. It’s been great. It’s a bit daunting starting somewhere new, though.
Nathan: Yes and it’s always difficult to remember everyone’s name. Has Roger introduced you around? (…… various small talk to build rapport interspersed with more trust-building.)
Nathan: …Emma Jones is very nice in HR if you need any help with that side of things.
Sarah: Yes, Emma did my HR interview for the job.
Nathan: Well, I better run through the security presentation with you. Do you have your email open? I’ll send you the security presentation now and I can talk you through it.
Sarah: OK, I see the email.
Nathan: OK, just double click on the “Security Presentation.zip” attachment.
Sarah: It has come up with WinZip.
Nathan: Just click extract and double-click on “Security Presentation”
Sarah: OK. …
Most bad guys pose as tech support
Social engineering gets inside your mind
It’s important to note that this simulated hacker pretended to be an employee of the I.T. department where the victim worked. According to security specialists at Wordfence.com, this is very common.
“… the majority of pretexts are a social engineer claiming to be some form of internal IT support. If someone calls you, claims to be someone you trust and appears to already know a lot about their subject, don’t trust them without verifying who they are. Sometimes this can be challenging because it is difficult to say no to a live human being on the phone. The social engineer knows this and may play on your emotions. They may tell you that they’re at the end of their shift and just need to ‘wrap this up’ before they can go home to their kids. Don’t fall for it.” —Wordfence.com
Wordfence.com suggests ways to politely maintain security while handling a call: If someone calls you, offer to call back. Ask them for their name and their main switchboard number (or front-desk) and an extension.
Once you have hung up, research the number they offered before you call it. Do a Google search of the number. You can also try WhitePages reverse phone lookup.
If the number and other information they give you checks out, instead of immediately calling them back, search for the company’s main number yourself. Then call them directly. Ask if they have been trying to contact you. Remember that the best social engineers have dedicated numbers with automated recordings that sound real. So, a bit of paranoia helps in this case.
If a hacker ‘social engineer’ succeeds
Management must be careful about punishing employees who have been deceived by hackers. This is usually counter-productive.
“Where there is blame, open minds close, inquiry tends to cease, and the desire to understand the whole system diminishes. When people work in an atmosphere of blame, they naturally cover up their errors and hide their real concerns.” —SystemsThinker.com
Two items about blame and accountability:
Moving from Blame to Accountability
…and this downloadable…
Pocket Guide: Moving from Blame to Accountability
Social engineering links
- Original HackerNoon article about social engineering is located here (new tab/window).
- Security specialists at Wordfence offer a nice collection of tips (new tab/window)
- Your security often also depends on reliable equipment and networks.
- Get a competitive advantage in the market with an improved web presence or Search Engine Optimization (SEO).
‘Friendly guy’ photo courtesy LinkedIn Sales Navigator on Unsplash
Gonzalez photo courtesy U.S. Secret Service

